Earlier this month, Intego (http://www.intego.com), a Mac security specialist, discovered the Mac Defender fake antivirus, which targets Mac users via SEO poisoning attacks (web sites set up to take advantage of search engine optimization tricks to get malicious sites to appear at the top of search results).
Since then, several variants have appeared: MacDefender, MacProtector and MacSecurity, all of which are the same application using different names. The goal of this fake antivirus software is to trick users into providing their credit card numbers to supposedly clean out infected files on their Macs.
Intego says it’s discovered a new variant of this malware that functions slightly differently. It comes in two parts.
The first part is a downloader, a tool that, after installation, downloads a payload from a web server. As with the Mac Defender malware variants, this installation package, called avSetup.pkg, is downloaded automatically when a user visits a specially crafted web site.
If Safari’s “Open ‘safe’ files after downloading” option is checked, the package will open Apple’s Installer, and the user will see a standard installation screen. If not, users may see the downloaded ZIP archive and double-click it out of curiosity, not remembering what they downloaded, then double-click the installation package. In either case, the Mac OS X Installer will launch.
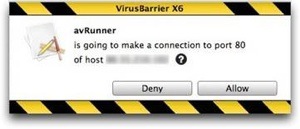
Unlike the previous variants of this fake antivirus, no administrator’s password is required to install this program. Since any user can install software in the Applications folder, a password is not needed. This package installs an application – the downloader – named avRunner, which then launches automatically. At the same time, the installation package deletes itself from the user’s Mac, so no traces of the original installer are left behind.
The second part of the malware is a new version of the MacDefender application called MacGuard. This is downloaded by the avRunner application from an IP address that is hidden in an image file in the avRunner application’s Resources folder. (The IP address is hidden using a simple form of steganography.)
Intego considers that the risk for this new variant to be medium, in part because the SEO poisoning has been very efficient in leading Mac users to booby-trapped pages, but also because no password is required to install this variant.
For further information about this fake antivirus and how it functions, see Intego’s Security Memo of May 2, 2011 describing the initial variant, Mac Defender. (http://blog.intego.com/may2)
Means of protection: the first thing to do is make sure that when seeing a web page that looks like a Finder window, and purports to be scanning your Mac, you know that this is bogus. Leave the page, and quit your web browser. If anything has downloaded, and the Installer application has opened, quit it right away; look in your Downloads folder for the file, then delete it. Next, users should uncheck the “Open ‘safe’ files after downloading” option in Safari’s General preferences.
VirusBarrier X6 (www.intego.com/virusbarrier/) protects users from this malware with malware definitions dated May 25, 2011, or later. VirusBarrier X6’s real-time scanner will detect the file when it is downloaded, and its Web Threats protection blocks web pages containing this malicious code. VirusBarrier Express and VirusBarrier.
Plus, available exclusively from the Mac App Store, detect this malware with malware definitions dated May 25, 2011 or later, but these programs don’t have a real-time scanner, due to limitations imposed by the Mac App Store; users should scan their Macs after they have updated to the latest malware definitions.